Ensuring Integrity in Data Migration Audits
Protecting Business Trust During Digital Transformation
In today’s digital-first environment, data migrations are no longer isolated IT activities—they are mission-critical business events. Whether driven by core system upgrades, cloud transformation, regulatory mandates, or mergers and acquisitions, data migration directly impacts financial accuracy, regulatory compliance, and customer trust. Yet, many organizations underestimate the risk. A single integrity failure during migration can lead to financial misstatements, regulatory findings, operational disruption, and long-term reputational damage. This is where data migration audits play a pivotal role—providing assurance that data remains accurate, complete, secure, and trustworthy throughout the transition.

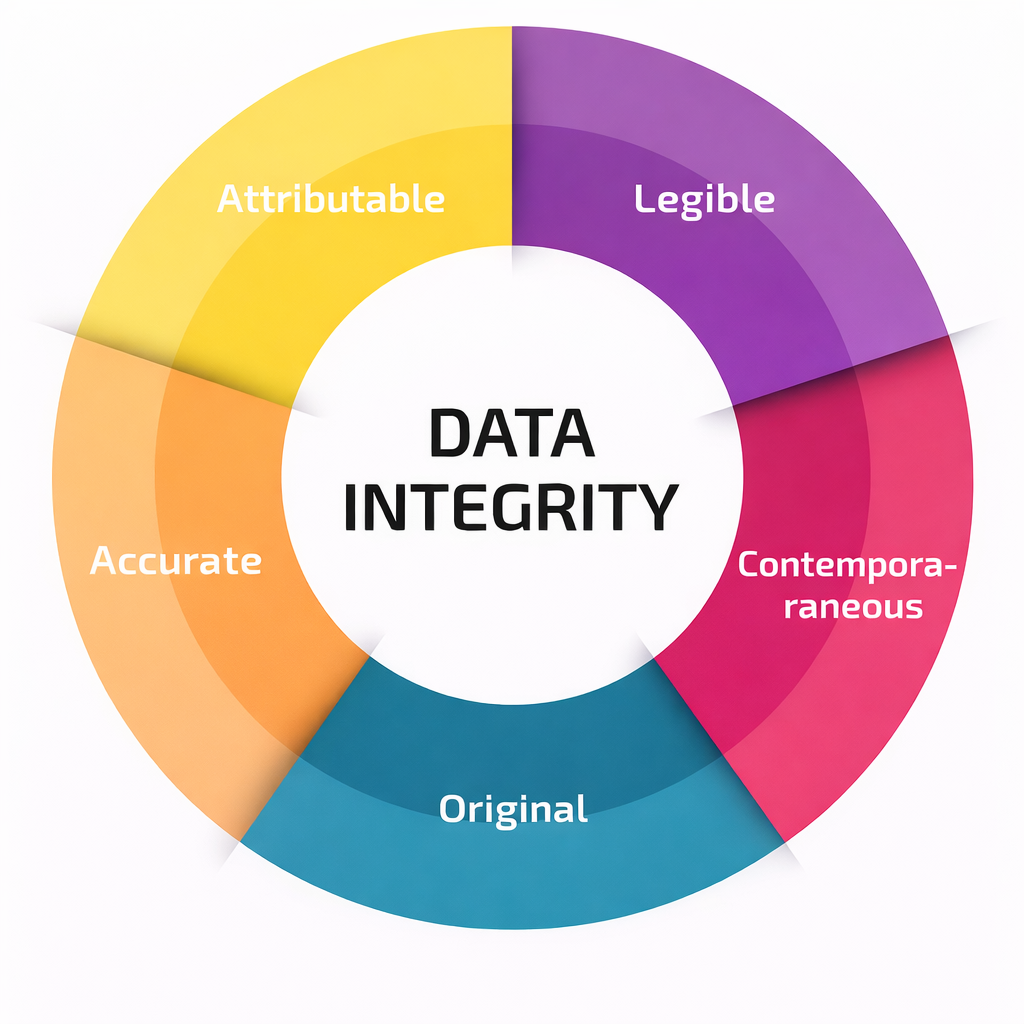
Why Data Integrity Is Non-Negotiable
Data integrity ensures that information remains unchanged, reliable, and fit for business use from source to target systems. During migration, data passes through multiple layers—extraction, transformation, validation, and loading—each creating potential exposure.
Without strong controls and independent oversight, organizations risk:
- Incomplete or corrupted datasets
- Unexplained discrepancies in financial and transactional records
- Loss of historical data and audit trails
- Non-compliance with regulatory and contractual obligations
- Erosion of stakeholder and customer confidence
A robust data migration audit ensures these risks are identified and addressed before they become business incidents.
Where Data Migrations Commonly Fail
From our audit experience, integrity breakdowns typically occur due to:
- Incomplete or Inaccurate TransfersMissing records, incorrect mappings, or transformation errors can quietly undermine data reliability often discovered only after go-live.
- Uncontrolled Data ChangesManual interventions, undocumented scripts, or weak segregation of duties increase the risk of unauthorized or irreversible data changes.
- Weak Security and Access ControlsExcessive privileges and poor monitoring during migration windows expose sensitive data to misuse or accidental modification.
- Inadequate Validation and ReconciliationRelying solely on high-level record counts without detailed reconciliations leaves critical discrepancies undetected.
- Poor AuditabilityLack of logs, approvals, and evidence makes it difficult to demonstrate compliance to auditors and regulators.
What a Strong Data Migration Audit Delivers
A well-designed data migration audit provides confidence that:
- All data is migrated completely and accurately
- Transformations are authorized, tested, and traceable
- Access is restricted, monitored, and accountable
- Discrepancies are identified, resolved, and documented
- Regulatory and internal control expectations are met
It transforms migration from a technical risk into a controlled, auditable, and defensible process.
Our Audit-Driven Approach to Data Migration Integrity
Our approach to data migration audits is grounded in risk-based governance, regulatory alignment, and practical execution assurance. We do not merely review technical steps—we assess whether the migration is controlled, auditable, and defensible from a business and compliance standpoint.
Strong Governance and Accountability
We begin by evaluating whether the data migration initiative is governed as a formal risk event rather than a standalone IT task. This includes assessing:
- Defined ownership and accountability across IT, business, and risk functions
- Approval mechanisms for migration scope, timelines, and critical datasets
- Integration of migration risks into enterprise risk management frameworks
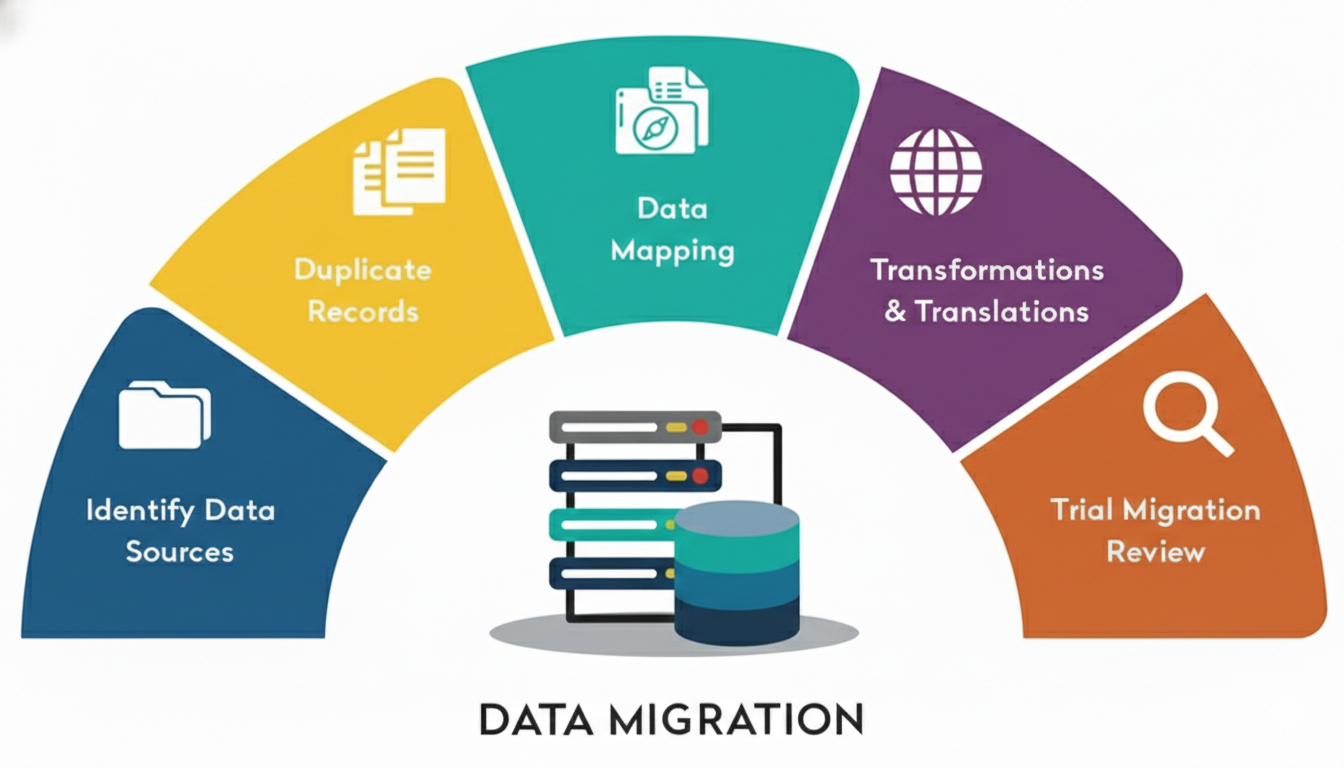
Data Mapping and Transformation Assurance
Data integrity is most vulnerable during transformation. Our audits validate that:
- Source-to-target mapping is comprehensive, accurate, and approved
- Transformation rules are documented, tested, and version-controlled
- Sensitive and regulated data elements are identified and protected
- Exceptions and overrides are tracked transparently
Security, Access, and Change Control Review
Migration windows often create elevated access risks. We assess whether:
- Least-privilege and role-based access is enforced
- Segregation of duties is maintained
- Privileged activities are logged and reviewed
- Changes follow formal change management
Reconciliation, Validation, and Business Sign-Off
We place strong emphasis on evidence-backed assurance, including:
- Pre- and post-migration reconciliations
- Integrity checks and control totals
- Independent business sign-off
- Clear documentation of discrepancies
Resilience, Rollback, and Post-Migration Assurance
Our audits examine preparedness for failure scenarios by reviewing:
- Backup and rollback strategies
- Mock migration and dry run results
- Post-migration monitoring controls
Built for Regulatory and Enterprise Expectations
Our data migration audit methodology is designed to meet the expectations of regulators, external auditors, internal audit teams, and senior management.
We align our assessments with:
- Enterprise risk management and internal control principles
- Information security and IT general control requirements
- Data protection, privacy, and confidentiality obligations
- Regulatory supervisory expectations across banking, financial services, insurance, and fintech sectors
By focusing on traceability, accountability, and evidence, we help organizations demonstrate that migration risks have been identified, controlled, and independently assured.
This approach not only supports compliance—it strengthens overall technology governance and audit readiness.
Common Gaps We Help Organizations Address
Through our engagements, we consistently observe recurring gaps that increase data migration risk. Our audits help organizations identify and remediate issues such as:
- Treating data migration as a technical activity with limited governance oversight
- Inadequate documentation of migration plans, mappings, and approvals
- Over-reliance on third-party vendors without sufficient independent review
- Weak reconciliation practices that focus only on record counts
- Delayed or minimal involvement of business data owners
- Insufficient logging and monitoring of migration activities
- Lack of structured post-migration reviews and assurance
By addressing these gaps early, organizations can significantly reduce the likelihood of post-implementation failures, audit findings, and regulatory observations.
Why Independent Assurance Matters
Data migration failures rarely make headlines—but their impact is often long-lasting. Independent audits provide early visibility into hidden risks, allowing organizations to remediate issues before they affect customers, regulators, or financial results.
A proactive audit approach protects:
- Business continuity
- Regulatory standing
- Customer confidence
- Brand reputation


